Access control has never been simpler or more affordable.
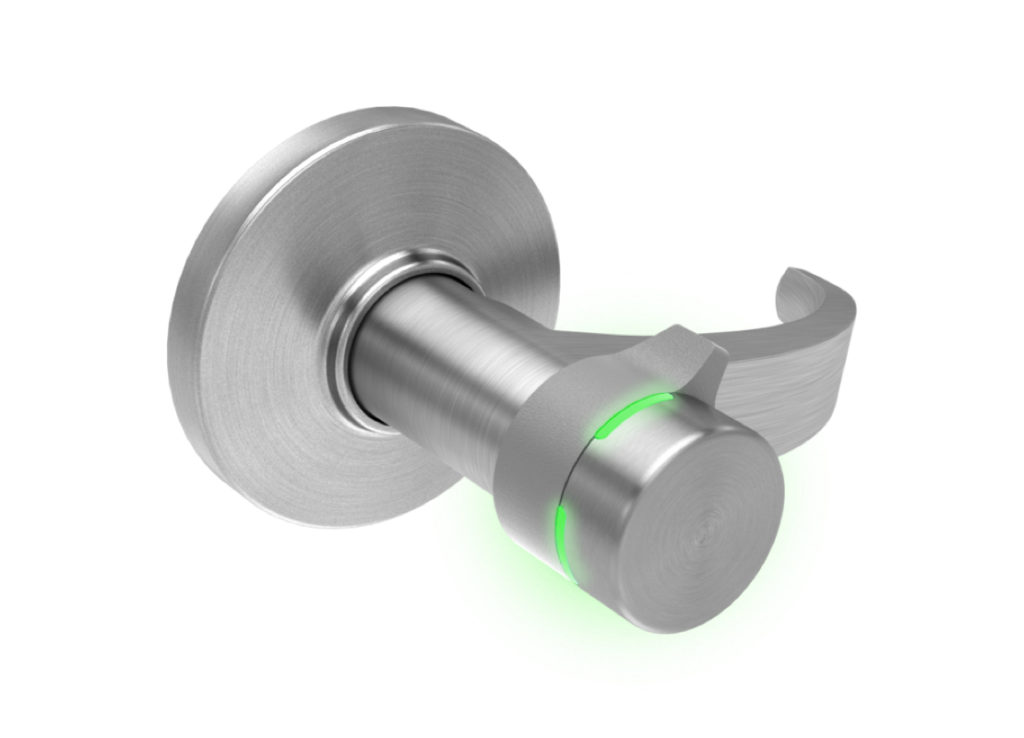
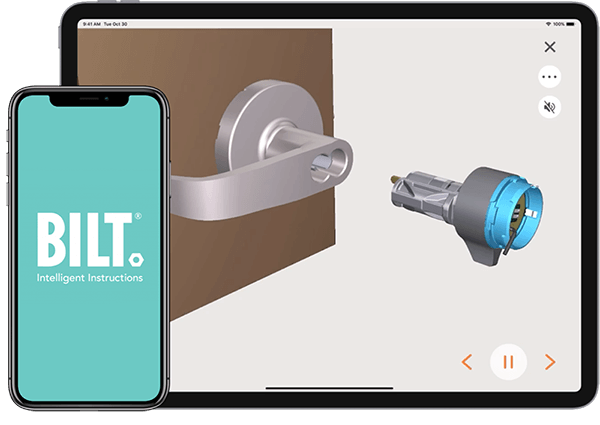
With Switch Tech, key management becomes a thing of the past. Access can be quickly and easily added to virtually any existing small format interchangeable core application. An easy-to-learn, easy-to-use app integrates seamlessly with existing access control systems and allows instantaneous, secure management of all users, plus visibility into who is accessing what, when.
It’s easy to make the switch.
Make the switch to greater control
Helpful Resources
Frequently Asked Questions
-
How do I get into the door if Switch Core breaks?
As with a standard core that gets compromised with a broken key, there are three ways to gain access if Switch Core fails.
- Drill out the core–this will take a high-power drill and carbide bit given that the core is made of hardened steel.
- The old “under the door tool”–this is a well-known trick by locksmiths and facility managers. They have a tool that slides under the door, swings up, and loops the interior handle of the door and opens it from the inside.
- Break into the door or whatever it is installed into.
-
Why is there an ongoing subscription for credentials?
BEST’s approach to Switch™ Tech credentials creates tremendous flexibility and scalability for administrators, particularly in organizations with dynamic access environments that include visitors, guests, contract labor, and frequent employee changes. Once credentials are licensed, admins can assign, unassign, blacklist, and reassign them to different users without any additional cost as often as they need to. And because Switch Deck integrates seamlessly with the customer’s access control system, that management can take place through the software the admins already know best and use most–their primary access control system. We strongly encourage our end users to license credentials in batches so they have extras available–it’s a minor expense for a significant gain in efficiency.
-
What is the role of Switch Bridge?
Due to the nature of access control, systems like Lenel or Genetec are often on-premise and function behind highly secure firewalls. Switch Bridge creates a secure link between BEST’s Switch Deck cloud software and the customer’s primary access control system. This enables greater efficiency and single-point, day-to-day management through the customer’s primary access control system without compromising security or creating vulnerabilities in the system.
-
What do I do with all of the doors that currently use RFID cards?
Perimeter doors that use RFID can be fitted with a Switch Tech Add-On Reader that can be used with the mobile app or fob. This allows a user to access the building as well as any doors equipped with Switch Core by using the mobile app or fob. Those employees who only require access to the building–and do not need to access doors equipped with Switch™ Tech–can continue to use their RFID card at the perimeter door. No need to switch the entire facility to Switch Tech on day one.
-
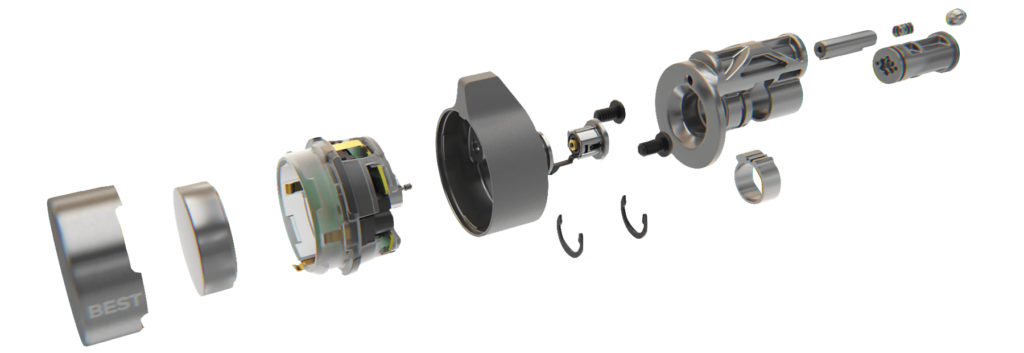
Is Switch Core durable? Can a person physically break this lock?
Switch Core has few moving parts and is built to withstand the abuse cores often get. Therefore, it isn’t the weak link in a given opening. It will be easier to break glass, kick in the door, or even break the entire lock off than to compromise Switch Core. Also, the core has been tested and exceeds ANSI standards for impact and abuse in terms of disabling the lock. Switch Core has no keyway to obstruct purposefully or accidentally.
-
If accessing the battery is so easy, can’t someone get to the core of the lock to break in?
Accessing the battery will not compromise security as the intelligence of the core is separated from the battery compartment by hardened steel. Further, access to the battery compartment requires a specific tool and is hidden with no obvious points of attack to help prevent tampering or vandalism.
-
Can someone hack in to get access?
Switch Core replaces a mechanical key and is actually more secure than keys and locks. Where keys can be duplicated or locks can be picked without direction, Switch Tech uses Bluetooth technology and encrypted credentials.
-
Does this meet ADA standards? How is it going to look on my doors?
It is ADA compliant as long as the lock it’s being installed into is also ADA compliant. From an aesthetic perspective, Switch Core integrates beautifully on mortise-and dead bolt-style locks because the core doesn’t protrude as it does on cylindrical hardware. But in truth, while it might seem a bit foreign at first on display cases or cylindrical locks, Switch Core quickly blends into decor once installed.